The following article explains what supply chain cybersecurity attacks look like in practice, why they’re accelerating, and how organizations can build repeatable, auditable supplier risk management frameworks aligned with ISO/IEC 27001, ISO 21434, NIS2, and the EU Cyber Resilience Act (CRA). As explored in the webinar, these attacks succeed because they exploit trusted relationships, creating access paths that can bypass many traditional perimeter controls.
You can jump to watch the webinar below, or keep reading for the key concepts, practical controls, and a self-assessment checklist to benchmark your current maturity.
Supply chain cybersecurity was once considered a procurement formality, limited to security questionnaires, contractual clauses, and certificates. But that approach no longer reflects how modern products and services are built, or how modern attackers operate.
Today, most organizations rely on complex ecosystems that include cloud platforms, managed service providers, embedded software vendors, open-source libraries, build tools, API services, device manufacturers, and specialist consultancies. The supply chain is now integral to operations and, because it is built on trust, presents a high-leverage target for attackers.
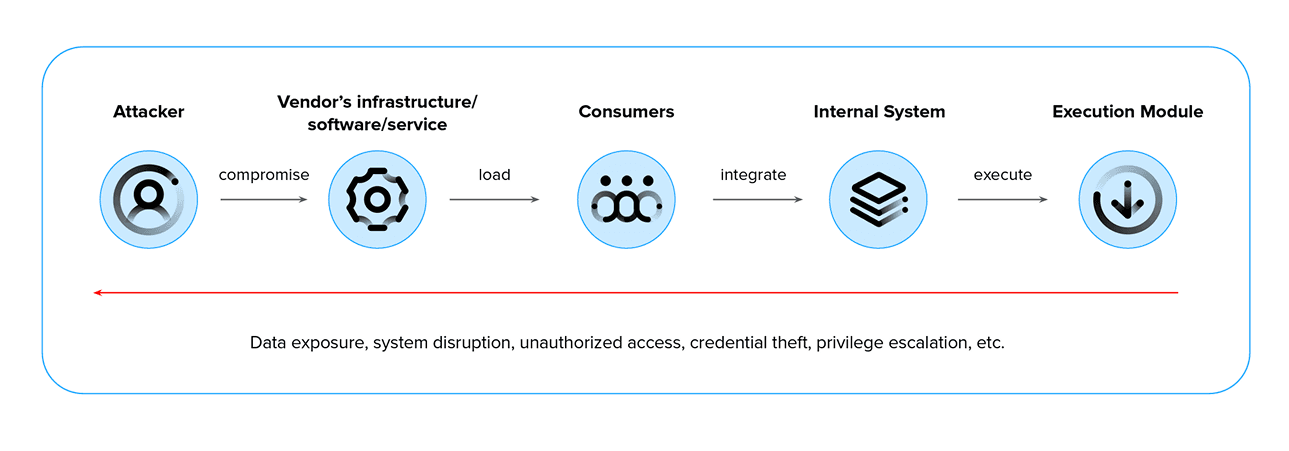
What is a supply chain cybersecurity attack?
A supply chain cyberattack occurs when bad actors compromise a trusted vendor, supplier, service provider, or software dependency, and then use that relationship as a back door to reach other organizations in the same supply chain (for example, the vendor’s customers, partners, or connected environments).
The defining characteristic is that attackers do not need to breach the target directly. They exploit trusted elements, such as legitimate software updates, third-party libraries, managed service accounts, or vendor support tools. Often, malicious activity appears normal at first, using signed packages, expected network paths, approved users, or routine system processes.
Why supply chain security is now a business imperative
Supply chain cybersecurity has moved beyond IT hygiene. Third-party risk management is now tied directly to financial impact, operational resilience, and regulatory exposure, especially in regulated industries like healthcare, automotive, and industrial manufacturing.
The potential impact is greater than ever
A single supplier compromise can affect dozens or even hundreds of downstream organizations. This risk increases when the supplier is integrated into shared layers such as CI/CD tools, identity providers, remote management solutions, widely used dependencies, or common libraries included in customer environments.
The costs are significant and often extend beyond IT
Even if direct financial losses are contained, additional impacts may include incident response expenses, service disruptions, increased audit and remediation efforts, contractual penalties, delayed releases, and reputational harm, especially in safety-critical and high-trust markets.
Top targeted industries and motives
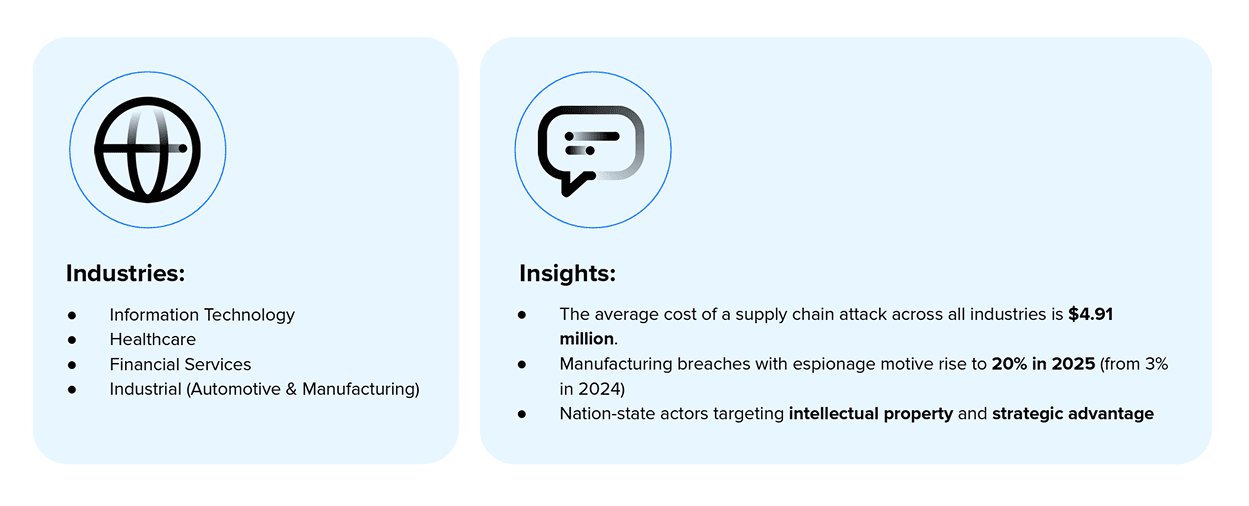
Motives and targets are evolving
Manufacturing and industrial environments are becoming more attractive to attackers, reflected in a growing number of breaches linked to espionage motives.
For organizations developing connected products, the risks are higher. A supply chain cybersecurity incident can compromise both internal IT networks and the integrity of products at customer sites.
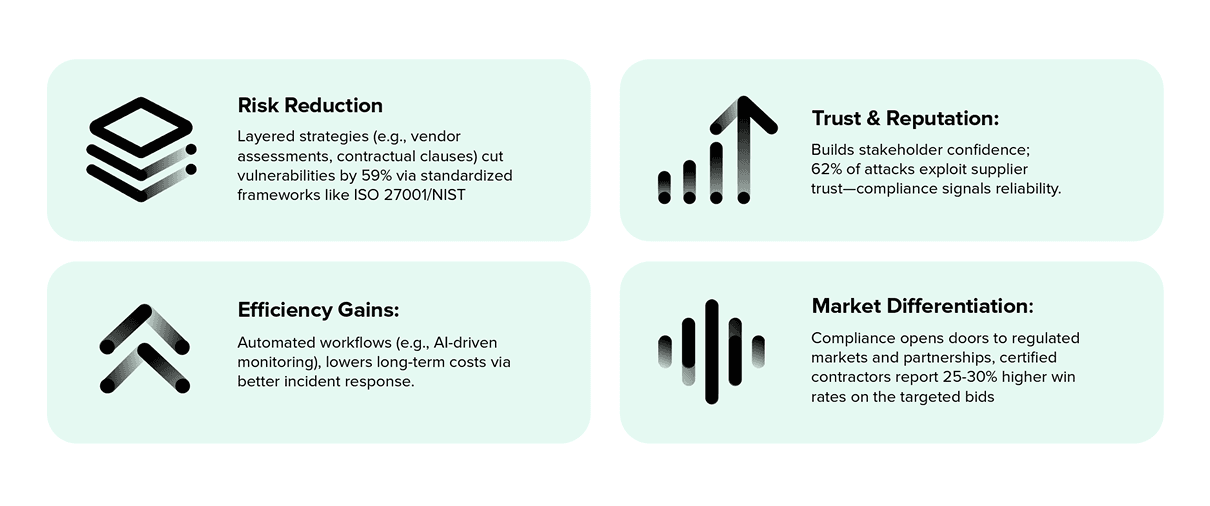
Compliance as a competitive advantage
A breach caused by a non-compliant vendor can trigger fines of up to 4% of global annual revenue under certain regulations. In addition, it may result in lawsuits, loss of intellectual property, and lasting damage to your brand.
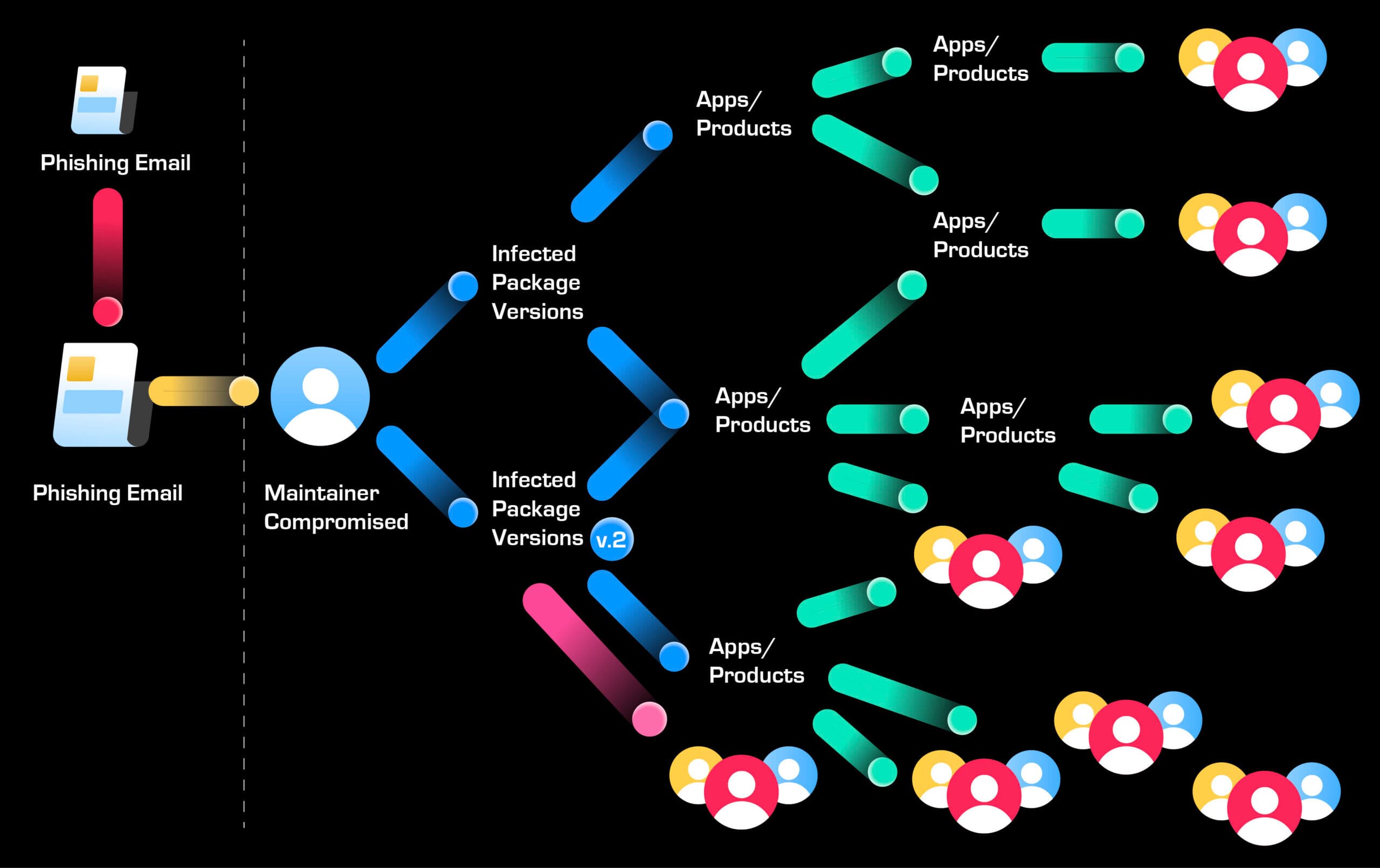
A real example: The node package manager (npm) supply chain attack
The specific incident matters less than the pattern it demonstrates: how quickly a single compromised identity in a supplier environment can push malicious code into downstream systems.
What happened:
- Attackers used a convincing phishing email (impersonating npm support) to compromise a maintainer account.
- Malicious versions of 19 widely used packages were published, including libraries with significant usage.
- The payload functioned as a browser-based crypto-stealer/wallet-drainer.
- Approximately $500 in stolen cryptocurrency, despite over 2.5 million downloads of the compromised packages.
Quick detection and response limited confirmed losses, but the exposure potential was substantial, given the package reach.
Why this matters outside of web development
The risk mechanics translate directly into regulated environments:
- Identity compromise scales. One account can publish artefacts consumed by many.
- Trust is inherited. Downstream teams may assume dependencies are safe because they’re popular, signed, or “standard.”
- Speed beats scrutiny. When delivery pressure is high, dependency review often becomes implicit rather than explicit.
- Detection is hard without baselines. If you don’t know what “normal” looks like (SBOMs, dependency registers, release provenance), anomalies blend into background noise.
In the webinar, Maksym walks through this pattern, explaining why a single compromised identity can quickly scale across downstream environments. If you’re building evidence for audits, it’s a useful reference point for what “normal” should look like in your dependency chain.
One phish, many victims: How a single compromise spreads
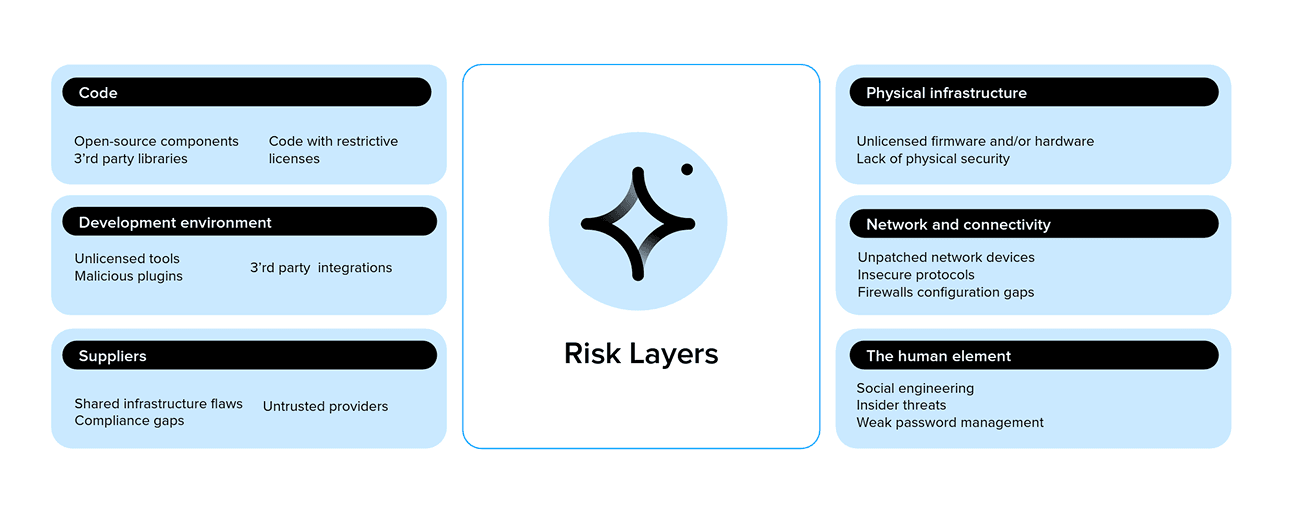
Where risk hides across the supplier ecosystem
Supply chain cybersecurity extends beyond vendor due diligence. It includes areas outside procurement’s control, such as internal engineering decisions and operational practices.
These risks can be categorized into layers:
- Code and dependencies (open source components, third-party libraries, licensing risk)
- Development environment (tools, plugins, misconfiguration, unmanaged assets)
- Suppliers and shared infrastructure (cloud services, managed IT, outsourced operations)
- Network and connectivity (unpatched devices, insecure protocols, firewall, and access issues)
- The human element (phishing, insider risk, weak password/access practices)
This layered approach helps teams avoid viewing supplier cybersecurity risk as merely a document-collection task. A supplier may appear fully compliant on paper yet still introduce risk through excessive access permissions, lack of transparency with subcontractors, inadequate build processes, or insufficient incident response coordination.
The third-party risk environment
Understanding a software organization's risk profile requires analyzing every layer of its digital ecosystem, extending beyond direct vendors to all underlying components and services.
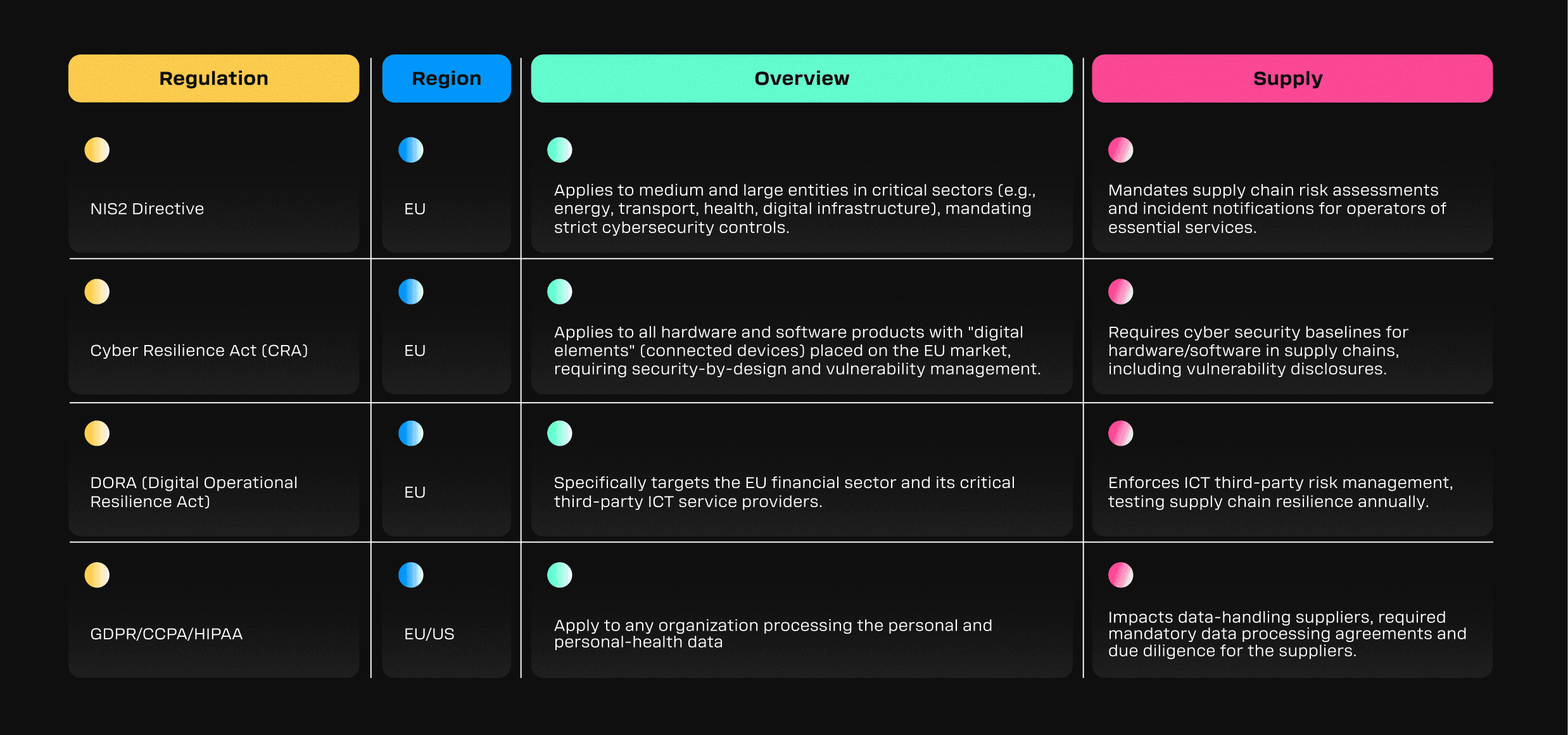
Compliance drivers: what regulations and standards expect
Supply chain cybersecurity for regulated industries has shifted from best practice to a compliance requirement, particularly for those operating in or selling to European markets.
Several regulations and frameworks define supply chain cybersecurity requirements, including:
- NIS2 (supply chain security risk management and incident readiness)
- EU Cyber Resilience Act (CRA) (security-by-design and vulnerability handling across the product lifecycle for products with digital elements)
- DORA (ICT third-party risk expectations in financial services)
- Broader data protection and security obligations where suppliers process regulated personal data (e.g., GDPR/HIPAA contexts)
Key EU and global regulations
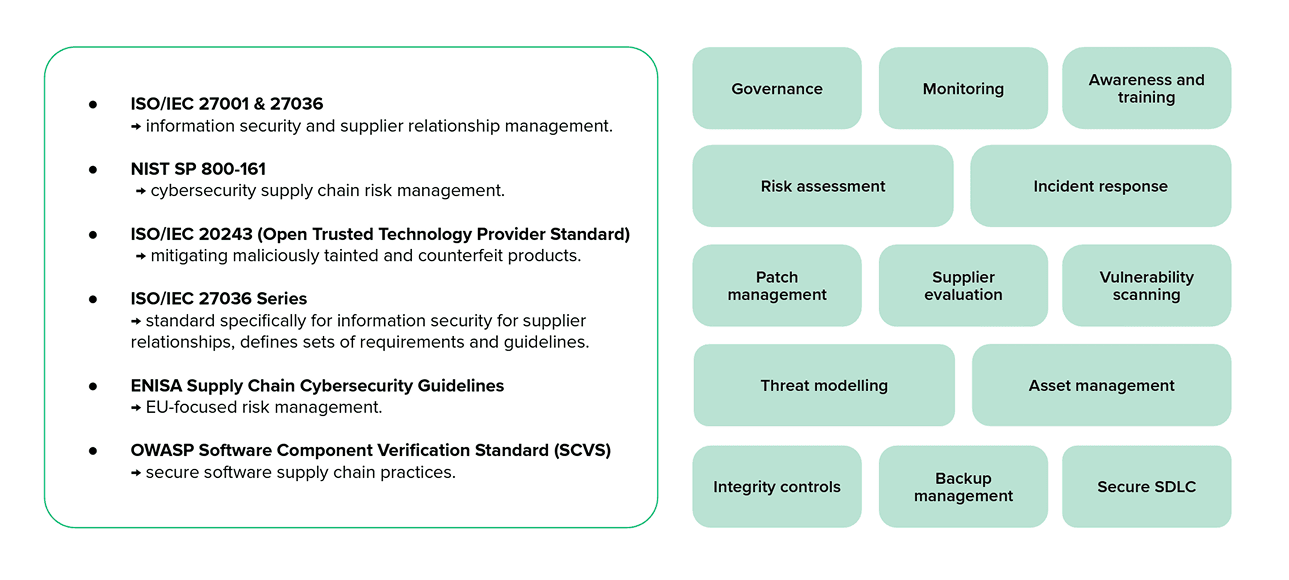
In addition to regulatory requirements, organizations can use established standards and guidance to structure supply chain cybersecurity controls, such as:
- ISO/IEC 27001 (ISMS foundation) and supplier-focused extensions such as ISO/IEC 27036
- NIST SP 800-161 (Cybersecurity Supply Chain Risk Management)
- ENISA supply chain guidance (EU-aligned approaches)
- OWASP SCVS (component verification practices)
Security standards and guidelines
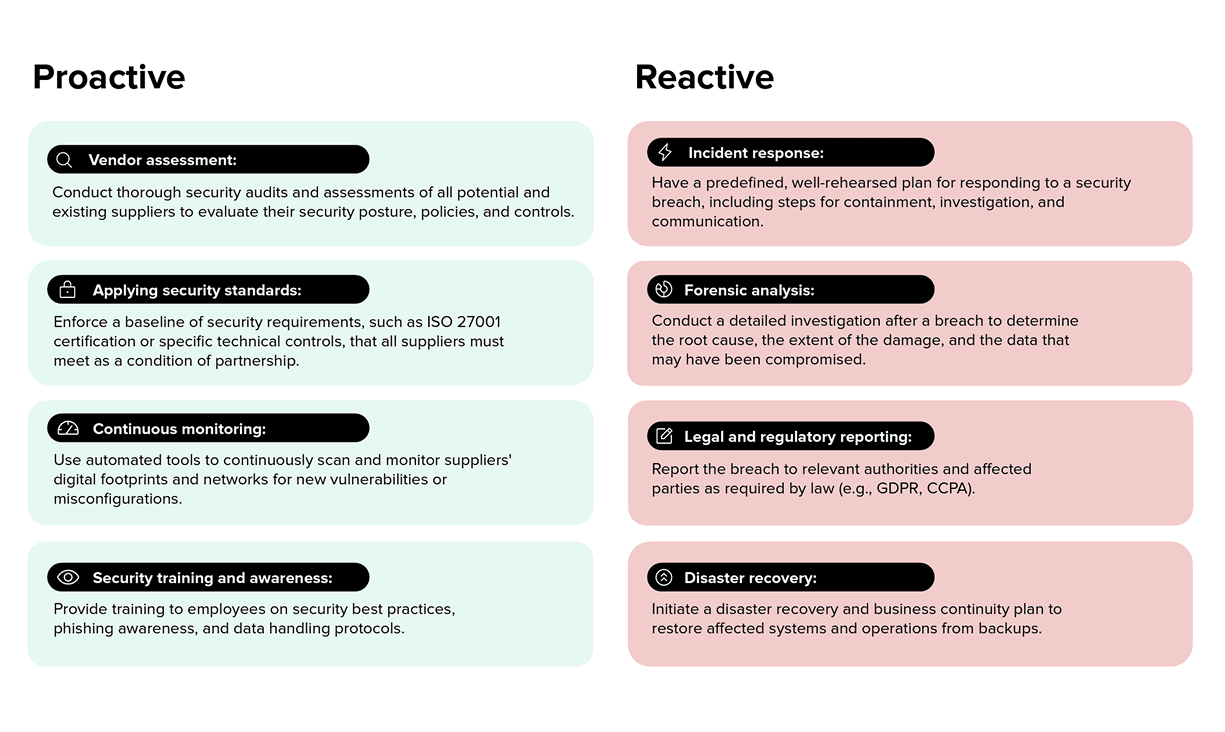
Proactive vs reactive security: why prevention changes the cost curve
Reactive organizations often address supplier cybersecurity risk only during procurement, audits, or incidents. In contrast, proactive organizations treat supplier cybersecurity risk as an ongoing program, integrating it into onboarding, continuous monitoring, governance, and evidence collection.
Building a lifecycle-based supplier security program with prioritized defense measures
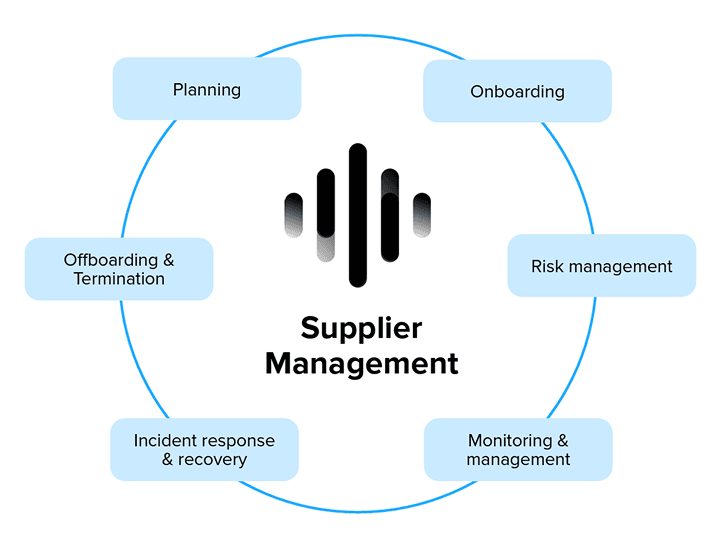
Supply chain security compliance is an ongoing process. Risks persist after supplier approval, as suppliers may change systems, personnel, subcontractors, and access levels, while new vulnerabilities may emerge. A structured supplier lifecycle typically includes the following phases:
Planning
- Define supplier security requirements and establish baseline controls
- Identify critical suppliers and categorize them by impact
- Assign internal ownership across security, procurement, engineering, and compliance teams
Onboarding
- Collect relevant evidence, such as certifications, policies, and technical validation where appropriate
- Establish contractual obligations, including incident notification, right-to-audit, and vulnerability disclosure expectations
- Implement access boundaries and apply least privilege principles
Monitoring
- Maintain continuous monitoring for vulnerabilities, changes in supplier security posture, and deviations from service level agreements
- Conduct periodic audits and assessments based on supplier tiering
- Monitor supplier compliance with evolving regulatory obligations
Incident response and recovery
- Establish notification timelines and escalation procedures
- Align response playbooks, specifying required evidence, forensic leadership, and containment procedures
- Prepare for recovery and continuity, including potential supply interruption scenarios
Offboarding
- Revoke access and verify the return or deletion of data
- Provide evidence of document closure to ensure audit readiness
- Capture lessons learned to inform future supplier selection and improve controls
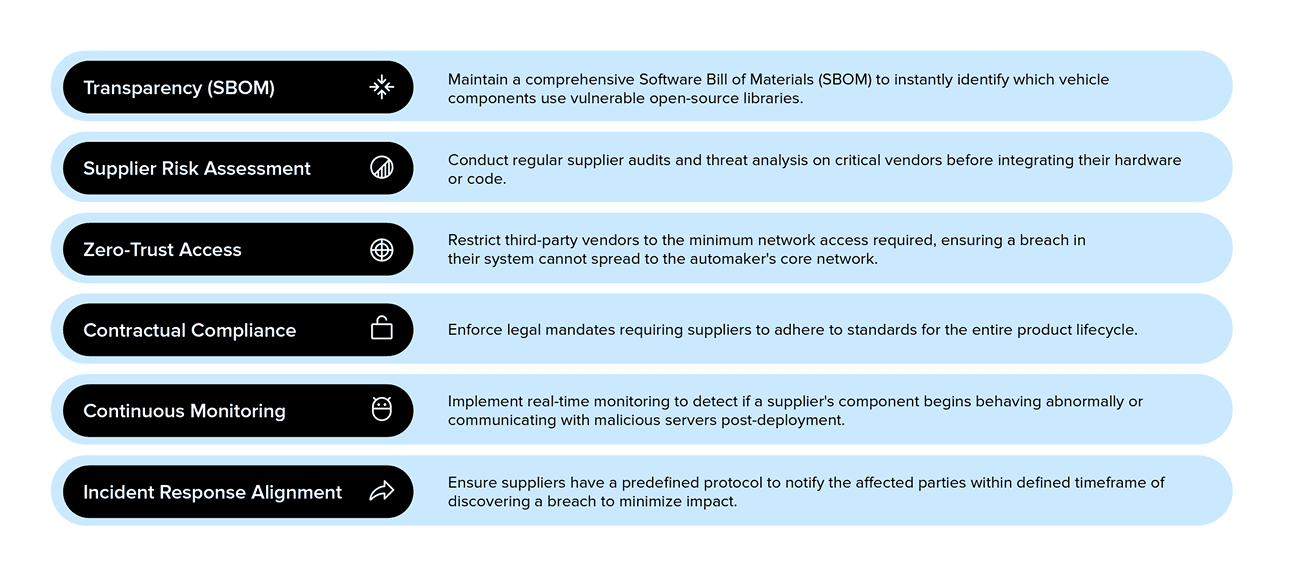
Six defense factors to prioritize
To translate frameworks into action, focus on defense factors that consistently appear in regulations and standards.
- Transparency and inventory - Effective management requires visibility. Supplier registers and software bills of materials (SBOMs) help organizations identify dependencies and potential vulnerabilities.
- Supplier risk assessment - Not all suppliers require the same level of scrutiny. Tiering allows you to allocate resources appropriately, focusing audits and validation on high-impact suppliers.
- Access controls - Broad, persistent supplier access increases the risk of incident spread. Strong boundary controls help contain potential impacts.
- Contractual governance - Contracts should reflect operational requirements, including incident notification timelines, vulnerability disclosure expectations, audit rights, and subcontractor transparency.
- Continuous monitoring - Continuous monitoring bridges the gap between approved suppliers and their current security posture. It enables detection of new vulnerabilities, unusual access patterns, and deviations.
- Incident response alignment - Incident response often suffers from unclear roles, delayed notifications, and incomplete evidence. Pre-agreed playbooks improve coordination and reduce confusion during critical moments.
Supply chain defense factors
The webinar focuses on turning these requirements into an operating rhythm: clear supplier tiering, defined control expectations, and evidence you can produce on demand. The checklist below helps you benchmark where you are today.
Download: Supply Chain Cybersecurity Self-Assessment Checklist
Use this checklist to benchmark your cybersecurity maturity, uncover gaps, and prioritize next steps across supplier inventory, onboarding, monitoring, and incident readiness.
Turn supply chain cybersecurity into practical, audit-ready progress
Supply chain cybersecurity programs often fail by operating at too high a level, with policies that aren’t practical to implement, or by becoming overly tactical, relying on tools and questionnaires without the governance, structure, and evidence needed to support compliance.
Star helps regulated organizations bridge this gap. We translate security frameworks into practical, scalable programs that align with product development, supplier ecosystems, and regulatory requirements.
We support you by implementing frameworks and standards such as ISO/IEC 27001, ISO 21434, NIS2, and the Cyber Resilience Act (CRA). Our services include building an Information Security Management System (ISMS) tailored to your operating model, establishing control frameworks and lifecycle-based cybersecurity governance, and delivering information security assessments with hands-on implementation support.
Whether you are formalizing your program for the first time or strengthening existing controls, Star can help you move from fragmented activities to a structured, audit-ready approach. Contact us to discuss your supply chain cybersecurity priorities.